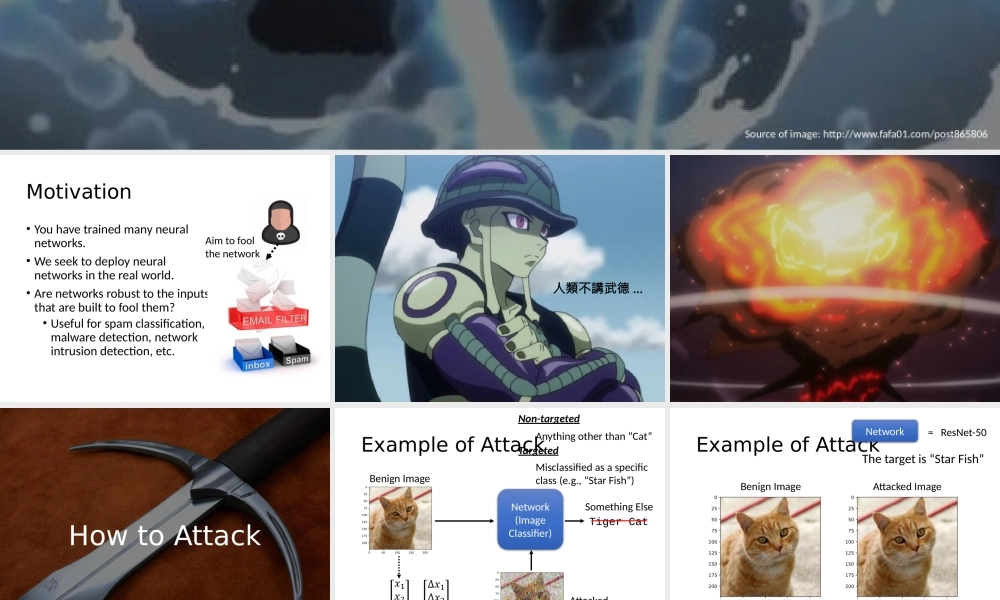
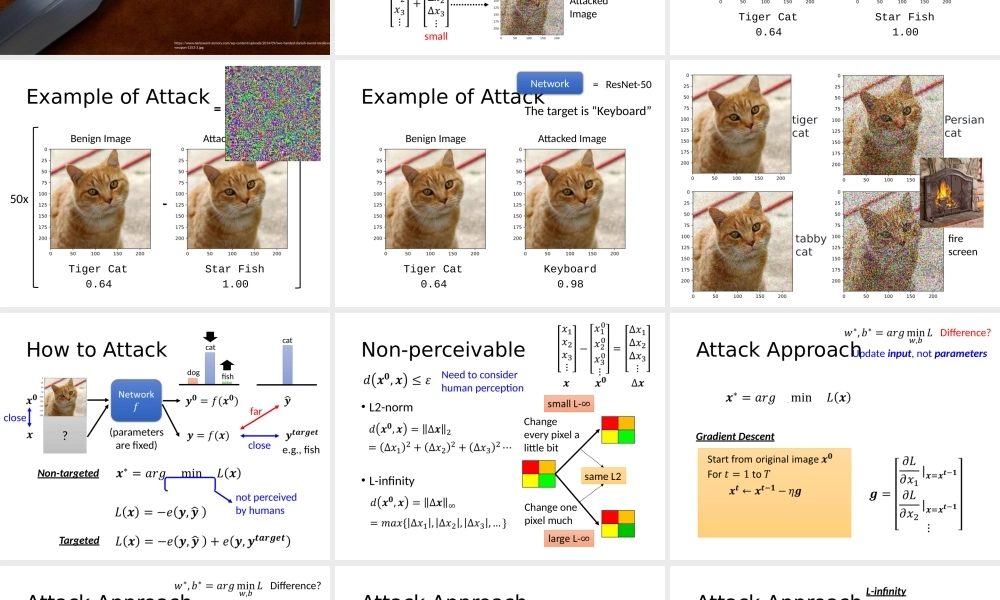
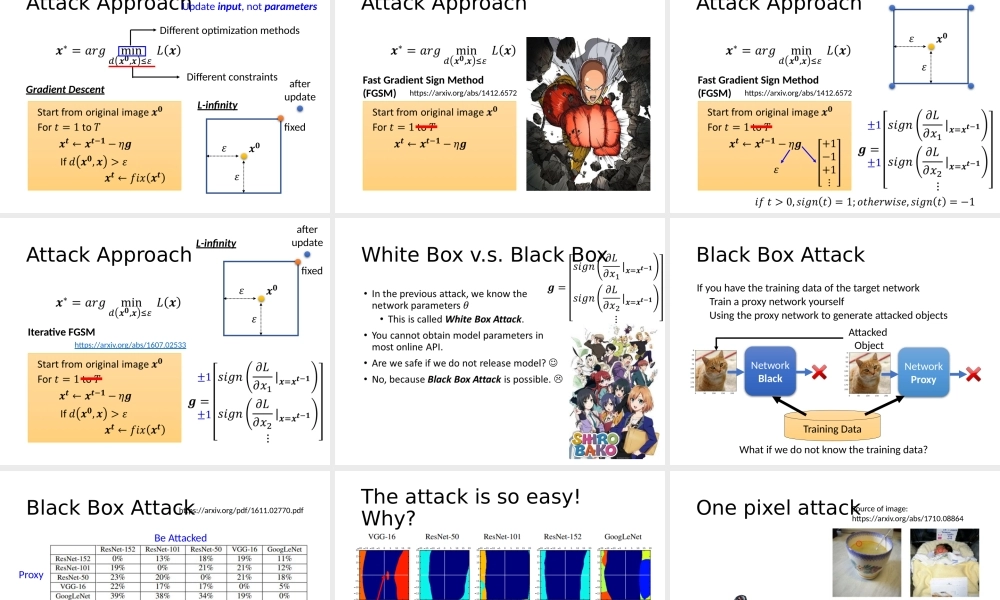
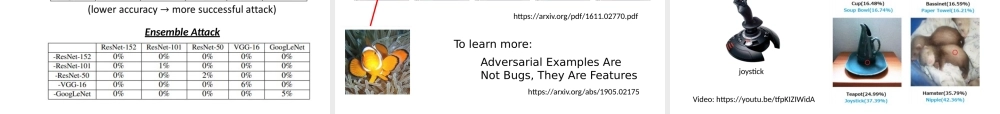
AdversarialAttackHung-yiLeeSourceofimage:http://www.fafa01.com/post865806Motivation•Youhavetrainedmanyneuralnetworks.•Weseektodeployneuralnetworksintherealworld.•Arenetworksrobusttotheinputsthatarebuilttofoolthem?•Usefulforspamclassification,malwaredetection,networkintrusiondetection,etc.Aimtofoolthenetwork人類不講武德…HowtoAttackhttps://www.darksword-armory.com/wp-content/uploads/2014/09/two-handed-danish-sword-medievaweapon-1352-3.jpgExampleofAttackSomethingElseTigerCatNetwork(ImageClassifier)BenignImageAttackedImagesmallNon-targetedTargetedAnythingotherthan“Cat”Misclassifiedasaspecificclass(e.g.,“StarFish”)ExampleofAttackTigerCat0.64BenignImageAttackedImageStarFish1.00NetworkResNet-50=Thetargetis“StarFish”ExampleofAttackTigerCat0.64BenignImageAttackedImageStarFish1.00=-50xExampleofAttackTigerCat0.64BenignImageAttackedImageKeyboard0.98NetworkResNet-50=Thetargetis“Keyboard”tabbycatPersiancatfirescreentigercatHowtoAttackclosefarclose?dogcatfishcatNon-targetedTargetede.g.,fish(parametersarefixed)notperceivedbyhumansNon-perceivable•L2-norm•L-infinityChangeonepixelmuchChangeeverypixelalittlebitsameL2NeedtoconsiderhumanperceptionGradientDescentAttackApproachDifference?Updateinput,notparametersAttackApproachGradientDescentDifference?Updateinput,notparametersL-infinityafterupdatefixedDifferentconstraintsDifferentoptimizationmethodsAttackApproachFastGradientSignMethod(FGSM)https://arxiv.org/abs/1412.6572AttackApproachFastGradientSignMethod(FGSM)https://arxiv.org/abs/1412.6572L-infinityAttackApproachIterativeFGSMhttps://arxiv.org/abs/1607.02533L-infinityafterupdatefixedWhiteBoxv.s.BlackBox•BlackBoxAttackIfyouhavethetrainingdataofthetargetnetworkTrainaproxynetworkyourselfUsingtheproxynetworktogenerateattackedobjectsWhatifwedonotknowthetrainingdata?NetworkBlackNetworkProxyTrainingDataAttackedObjectBlackBoxAttackhttps://arxiv.org/pdf/1611.02770.pdfBeAttackedProxyEnsembleAttackTheattackissoeasy!Why?https://arxiv.org/pdf/1611.02770.pdfhttps://arxiv.org/abs/190...